Edge Delta Datadog Source
14 minute read
Overview
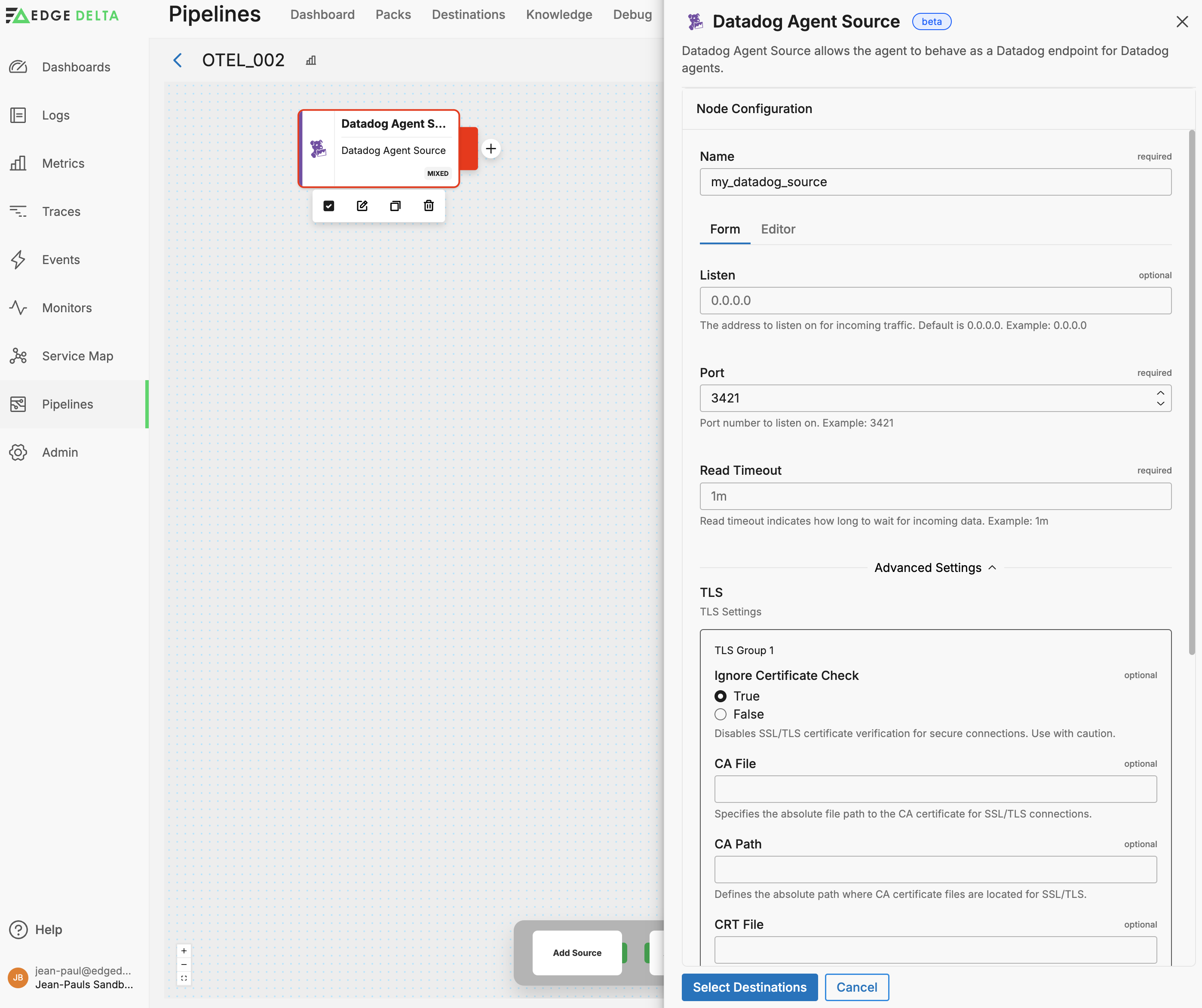
The Datadog Agent Source node enables the agent to ingest data types such as logs, metrics, and traces from the Datadog agent.
AI Team: Configure this source using the Datadog Agent connector for streamlined setup in AI Team.
Example Configuration
In this example, the port parameter indicates the network port on which the node will listen for incoming data. This port needs to be open and available for the node to accept incoming connections from Datadog agents. The read_timeout specifies the maximum duration the node will wait for incoming data before timing out. This helps manage timeouts and ensures that the node doesn’t hang indefinitely if no data arrives. The tls block contains configurations related to Transport Layer Security (TLS), which is used for securing connections: the ignore_certificate_check parameter indicates whether SSL/TLS certificate verification should be disabled. It is set to false, which means that the node will verify certificates as part of securing the connection. This is important for ensuring a secure data transfer channel.
nodes:
- name: my_datadog_source
type: datadog_agent_input
port: 3421
read_timeout: 1m
tls:
ignore_certificate_check: false
Reconfiguring Datadog Agents
After configuring the Datadog Agent Source node in your Edge Delta pipeline, you must reconfigure your Datadog agents to send data to Edge Delta instead of the Datadog backend.
For Datadog Agents on Servers
Edit /etc/datadog-agent/datadog.yaml to route telemetry to the Edge Delta agent’s Datadog Agent Source node:
dd_url: http://<edge-delta-host>:<port>
apm_config:
apm_dd_url: http://<edge-delta-host>:<port>
Replace <edge-delta-host> with the address of your Edge Delta agent and <port> with the port configured on the Datadog Agent Source node (for example, 3421).
Restart the agent: sudo systemctl restart datadog-agent
For DogStatsD Client Libraries
Python:
from datadog import initialize
initialize(statsd_host='edge-delta-host', statsd_port=3421)
Node.js:
const StatsD = require('node-statsd');
const client = new StatsD('edge-delta-host', 3421);
For Datadog APM Libraries
Java: Add JVM arguments:
-Ddd.agent.host=edge-delta-host -Ddd.agent.port=3421
Python:
from ddtrace import tracer
tracer.configure(hostname='edge-delta-host', port=3421)
Go:
tracer.Start(tracer.WithAgentAddr("edge-delta-host:3421"))
Required Parameters
name
A descriptive name for the node. This is the name that will appear in pipeline builder and you can reference this node in the YAML using the name. It must be unique across all nodes. It is a YAML list element so it begins with a - and a space followed by the string. It is a required parameter for all nodes.
nodes:
- name: <node name>
type: <node type>
type: datadog_agent_input
The type parameter specifies the type of node being configured. It is specified as a string from a closed list of node types. It is a required parameter.
nodes:
- name: <node name>
type: <node type>
Port
The port parameter specifies the port number to listen on. It is specified as an integer and is required.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
Optional Parameters
disabled
The disabled parameter disables the node in the pipeline. When set to true, the agent ignores the node at startup. You can toggle nodes on or off in the pipeline builder. It is specified as a boolean, defaults to false, and is optional.
nodes:
- name: <node name>
type: <node type>
disabled: true
listen
The listen parameter specifies the address to listen on for incoming traffic. The default value is 0.0.0.0, and it is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
listen: <host>
read_timeout
The read_timeout parameter indicates how long to wait for incoming data before timing out. It is specified as a duration and is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
read_timeout: <duration>
rate_limit
The rate_limit parameter enables you to control data ingestion based on system resource usage. This advanced setting helps prevent source nodes from overwhelming the agent by automatically throttling or stopping data collection when CPU or memory thresholds are exceeded.
Use rate limiting to prevent runaway log collection from overwhelming the agent in high-volume sources, protect agent stability in resource-constrained environments with limited CPU/memory, automatically throttle during bursty traffic patterns, and ensure fair resource allocation across source nodes in multi-tenant deployments.
When rate limiting triggers, pull-based sources (File, S3, HTTP Pull) stop fetching new data, push-based sources (HTTP, TCP, UDP, OTLP) reject incoming data, and stream-based sources (Kafka, Pub/Sub) pause consumption. Rate limiting operates at the source node level, where each source with rate limiting enabled independently monitors and enforces its own thresholds.
Rate limiting vs backpressure: Rate limiting and backpressure are different mechanisms. Rate limiting controls data ingestion at the source based on CPU or memory thresholds. Backpressure controls data output at the destination when in-memory queues fill up. Backpressure logs such as
backpressure: dataCh at 92% capacitydo not appear when rate limiting triggers, and rate limiting logs do not appear during backpressure events.
Observability: When rate limiting is active in enforce mode, the agent does not produce INFO, WARN, or ERROR level logs. To confirm that rate limiting is triggering, check the source node’s Bytes I/O metrics in the Edge Delta app for gaps or drops that coincide with expected throttling periods.
Configuration Steps:
- Click Add New in the Rate Limit section
- Click Add New for Evaluation Policy
- Select Policy Type:
- CPU Usage: Monitors CPU consumption and rate limits when usage exceeds defined thresholds. Use for CPU-intensive sources like file parsing or complex transformations.
- Memory Usage: Monitors memory consumption and rate limits when usage exceeds defined thresholds. Use for memory-intensive sources like large message buffers or caching.
- AND (composite): Combines multiple sub-policies with AND logic. All sub-policies must be true simultaneously to trigger rate limiting. Use when you want conservative rate limiting (both CPU and memory must be high).
- OR (composite): Combines multiple sub-policies with OR logic. Any sub-policy can trigger rate limiting. Use when you want aggressive rate limiting (either CPU or memory being high triggers).
- Select Evaluation Mode. Choose how the policy behaves when thresholds are exceeded:
- Enforce (default): Actively applies rate limiting when thresholds are met. Pull-based sources (File, S3, HTTP Pull) stop fetching new data, push-based sources (HTTP, TCP, UDP, OTLP) reject incoming data, and stream-based sources (Kafka, Pub/Sub) pause consumption. Use in production to protect agent resources.
- Monitor: Logs when rate limiting would occur without actually limiting data flow. Use for testing thresholds before enforcing them in production.
- Passthrough: Disables rate limiting entirely while keeping the configuration in place. Use to temporarily disable rate limiting without removing configuration.
- Set Absolute Limits and Relative Limits (for CPU Usage and Memory Usage policies)
Note: If you specify both absolute and relative limits, the system evaluates both conditions and rate limiting triggers when either condition is met (OR logic). For example, if you set absolute limit to
1.0CPU cores and relative limit to50%, rate limiting triggers when the source uses either 1 full core OR 50% of available CPU, whichever happens first.
For CPU Absolute Limits: Enter value in full core units:
0.1= one-tenth of a CPU core0.5= half a CPU core1.0= one full CPU core2.0= two full CPU cores
For CPU Relative Limits: Enter percentage of total available CPU (0-100):
50= 50% of available CPU75= 75% of available CPU85= 85% of available CPU
For Memory Absolute Limits: Enter value in bytes
104857600= 100Mi (100 × 1024 × 1024)536870912= 512Mi (512 × 1024 × 1024)1073741824= 1Gi (1 × 1024 × 1024 × 1024)
For Memory Relative Limits: Enter percentage of total available memory (0-100)
60= 60% of available memory75= 75% of available memory80= 80% of available memory
- Set Refresh Interval (for CPU Usage and Memory Usage policies). Specify how frequently the system checks resource usage:
- Recommended Values:
10sto30sfor most use cases5sto10sfor high-volume sources requiring quick response1mor higher for stable, low-volume sources
The system fetches current CPU/memory usage at the specified refresh interval and uses that value for evaluation until the next refresh. Shorter intervals provide more responsive rate limiting but incur slightly higher overhead, while longer intervals are more efficient but slower to react to sudden resource spikes.
The GUI generates YAML as follows:
# Simple CPU-based rate limiting
nodes:
- name: <node name>
type: <node type>
rate_limit:
evaluation_policy:
policy_type: cpu_usage
evaluation_mode: enforce
absolute_limit: 0.5 # Limit to half a CPU core
refresh_interval: 10s
# Simple memory-based rate limiting
nodes:
- name: <node name>
type: <node type>
rate_limit:
evaluation_policy:
policy_type: memory_usage
evaluation_mode: enforce
absolute_limit: 536870912 # 512Mi in bytes
refresh_interval: 30s
Composite Policies (AND / OR)
When using AND or OR policy types, you define sub-policies instead of limits. Sub-policies must be siblings (at the same level)—do not nest sub-policies within other sub-policies. Each sub-policy is independently evaluated, and the parent policy’s evaluation mode applies to the composite result.
- AND Logic: All sub-policies must evaluate to true at the same time to trigger rate limiting. Use when you want conservative rate limiting (limit only when CPU AND memory are both high).
- OR Logic: Any sub-policy evaluating to true triggers rate limiting. Use when you want aggressive protection (limit when either CPU OR memory is high).
Configuration Steps:
- Select AND (composite) or OR (composite) as the Policy Type
- Choose the Evaluation Mode (typically Enforce)
- Click Add New under Sub-Policies to add the first condition
- Configure the first sub-policy by selecting policy type (CPU Usage or Memory Usage), selecting evaluation mode, setting absolute and/or relative limits, and setting refresh interval
- In the parent policy (not within the child), click Add New again to add a sibling sub-policy
- Configure additional sub-policies following the same pattern
The GUI generates YAML as follows:
# AND composite policy - both CPU AND memory must exceed limits
nodes:
- name: <node name>
type: <node type>
rate_limit:
evaluation_policy:
policy_type: and
evaluation_mode: enforce
sub_policies:
# First sub-policy (sibling)
- policy_type: cpu_usage
evaluation_mode: enforce
absolute_limit: 0.75 # Limit to 75% of one core
refresh_interval: 15s
# Second sub-policy (sibling)
- policy_type: memory_usage
evaluation_mode: enforce
absolute_limit: 1073741824 # 1Gi in bytes
refresh_interval: 15s
# OR composite policy - either CPU OR memory can trigger
nodes:
- name: <node name>
type: <node type>
rate_limit:
evaluation_policy:
policy_type: or
evaluation_mode: enforce
sub_policies:
- policy_type: cpu_usage
evaluation_mode: enforce
relative_limit: 85 # 85% of available CPU
refresh_interval: 20s
- policy_type: memory_usage
evaluation_mode: enforce
relative_limit: 80 # 80% of available memory
refresh_interval: 20s
# Monitor mode for testing thresholds
nodes:
- name: <node name>
type: <node type>
rate_limit:
evaluation_policy:
policy_type: memory_usage
evaluation_mode: monitor # Only logs, doesn't limit
relative_limit: 70 # Test at 70% before enforcing
refresh_interval: 30s
channel_size
The channel_size parameter sets the size of the internal data channel buffer. It is specified as an integer, has a default of 1000, and is optional.
parallel_worker_count
The parallel_worker_count parameter sets the number of workers that process incoming data in parallel. It is specified as an integer, has a default of 2, and is optional.
source_metadata
This option is used to define which detected resources and attributes to add to each data item as it is ingested by Edge Delta. You can select:
- Required Only: This option includes the minimum required resources and attributes for Edge Delta to operate.
- Default: This option includes the required resources and attributes plus those selected by Edge Delta
- High: This option includes the required resources and attributes along with a larger selection of common optional fields.
- Custom: With this option selected, you can choose which attributes and resources to include. The required fields are selected by default and can’t be unchecked.
Based on your selection in the GUI, the source_metadata YAML is populated as two dictionaries (resource_attributes and attributes) with Boolean values.
See Choose Data Item Metadata for more information on selecting metadata.
max_connections
Minimum Agent Version: v2.13.0
The max_connections parameter sets the maximum number of concurrent connections the server accepts. The server rejects new connections when this limit is reached. Set to 0 for unlimited. It is specified as an integer and is optional. The default is 0 (unlimited).
max_connections_per_ip
Minimum Agent Version: v2.13.0
The max_connections_per_ip parameter sets the maximum concurrent connections from a single IP address. Set to 0 for unlimited. It is specified as an integer and is optional. The default is 0 (unlimited).
read_buffer_size
Minimum Agent Version: v2.13.0
The read_buffer_size parameter sets the per-connection buffer size for reading request data. This also controls the maximum header size. Increase this value for large requests or decrease it to save memory. It is specified as a size and is optional. The default is 16KB.
write_buffer_size
Minimum Agent Version: v2.13.0
The write_buffer_size parameter sets the per-connection buffer size for writing response data. Increase this value for large responses or decrease it to save memory. It is specified as a size and is optional. The default is 4KB.
truncate_limit
Minimum Agent Version: v2.13.0
The truncate_limit parameter sets the maximum size for individual items. The server truncates items larger than this limit but smaller than drop_limit and records a metric in edgedelta_node_truncated_items. Set to nil or omit to disable truncation. It is specified as a size and is optional. The default is nil (disabled).
drop_limit
Minimum Agent Version: v2.13.0
The drop_limit parameter sets the maximum size for individual items. The server drops items larger than this limit and records a metric in edgedelta_node_dropped_items. When you set both limits, drop_limit must be greater than or equal to truncate_limit. It is specified as a size and is optional. The default is 128MB.
idle_timeout
The idle_timeout parameter sets how long the server keeps an idle connection open before closing it. It is specified as a duration and is optional. The default is 1m.
write_timeout
The write_timeout parameter sets how long the server waits to finish writing a response before timing out. It is specified as a duration and is optional. The default is 10s.
tls
The tls parameter is a dictionary type that enables a number of TLS options to be set using sub-parameters.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
<tls options>:
ca_file
The ca_file parameter is a child of the tls parameter. It specifies the CA certificate file. It is specified as a string and is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
ca_file: /certs/ca.pem
ca_path
The ca_path parameter is a child of the tls parameter. It specifies the location of the CA certificate files. It is specified as a string and is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
ca_path: <path>
client_auth_type
The client_auth_type parameter is a child of the tls parameter. It specifies the authentication type to use for the connection. It is specified as a string from a closed list and is optional.
The following authentication methods are available:
- noclientcert indicates that no client certificate should be requested during the handshake, and if any certificates are sent they will not be verified.
- requestclientcert indicates that a client certificate should be requested during the handshake, but does not require that the client send any certificates.
- requireanyclientcert indicates that a client certificate should be requested during the handshake, and that at least one certificate is required from the client, but that certificate is not required to be valid.
- verifyclientcertifgiven indicates that a client certificate should be requested during the handshake, but does not require that the client sends a certificate. If the client does send a certificate it is required to be valid.
- requireandverifyclientcert indicates that a client certificate should be requested during the handshake, and that at least one valid certificate is required to be sent by the client
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
client_auth_type: <auth type>
crt_file
The crt_file parameter is a child of the tls parameter. It specifies the certificate file. It is specified as a string and is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
crt_file: /certs/server-cert.pem
ignore_certificate_check
The ignore_certificate_check parameter is a child of the tls parameter. When set to true, it ignores certificate checks for the remote endpoint. It is specified as a Boolean value and the default is false, indicating that TLS verification will be performed. This is an optional parameter.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
ignore_certificate_check: true
key_file
The key_file parameter is a child of the tls parameter. It specifies the private key file. It is specified as a string and is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
key_file: /certs/server-key.pem
key_password
The key_password parameter is a child of the tls parameter. It specifies the key password. When the private key_file location is provided, this file can also be provided to get the password of the private key. It is specified as a string and is optional.
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
key_password: <password>
max_version
The max_version parameter is a child of the tls parameter. It specifies the maximum version of TLS to accept. It is specified as a string and is optional.
You can select one of the following options:
TLSv1_0TLSv1_1TLSv1_2TLSv1_3
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
max_version: <TLS version>
min_version
The min_version parameter is a child of the tls parameter. It specifies the minimum version of TLS to accept. It is specified as a string and is optional. The default is TLSv1_2.
You can select one of the following options:
TLSv1_0TLSv1_1TLSv1_2TLSv1_3
nodes:
- name: <node name>
type: datadog_agent_input
port: <port number>
tls:
min_version: <TLS version>