Deploying the Edge Delta Lambda Forwarder
8 minute read
Overview
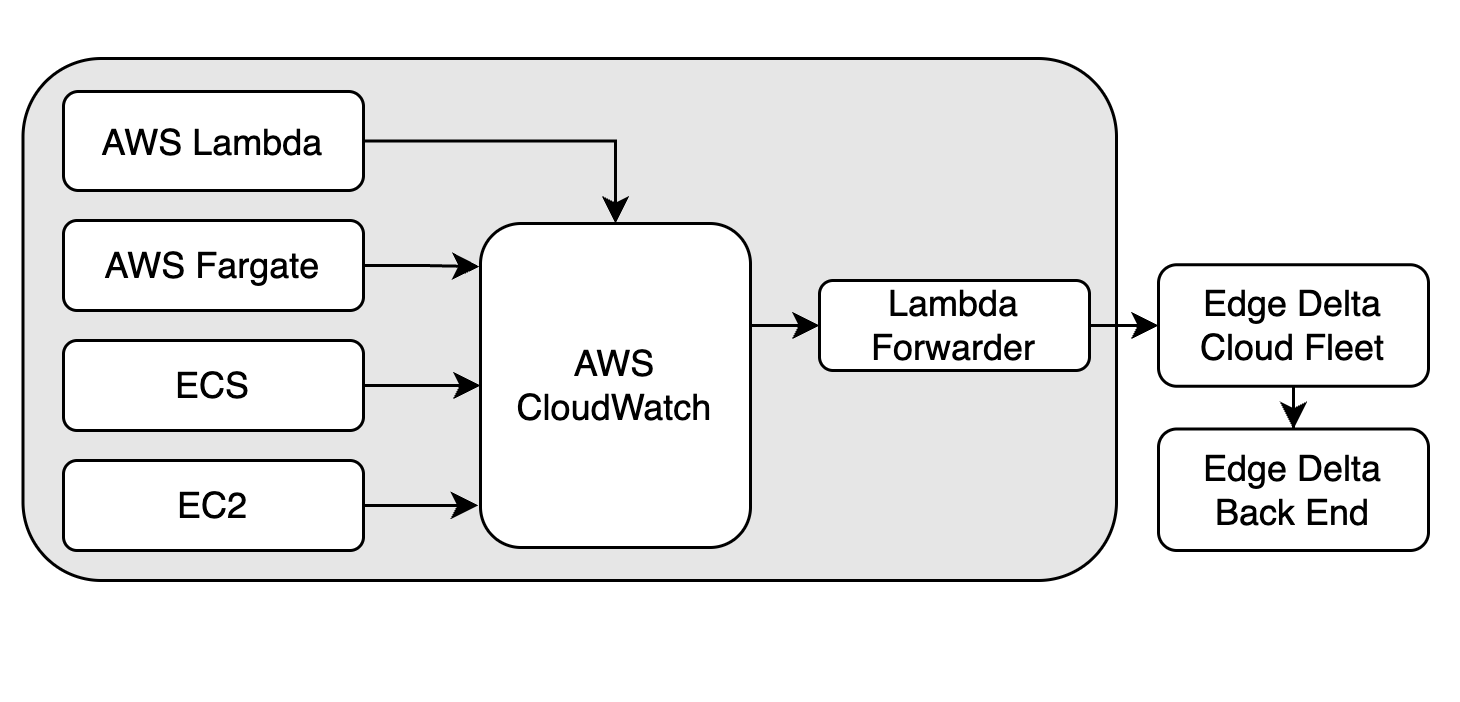
The Lambda Forwarder is a standalone Lambda function that collects logs from CloudWatch log groups and forwards them to an Edge Delta Cloud pipeline. It supports CloudWatch logs from any AWS service, including Lambda, ECS, EC2, WAF, RDS, and others. See Serverless AWS Monitoring for an overview and comparison with the Lambda Extension.
Use the Forwarder when you need to ingest CloudWatch logs from any AWS service. If you need to monitor a Lambda function’s own logs directly (without CloudWatch), see the Lambda Extension instead.
Prerequisites
Before you begin, make sure you have:
- An Edge Delta account with access to create Cloud pipelines
- AWS CLI configured with credentials that have permission to deploy Lambda functions
- The name or ARN of the CloudWatch log group you want to forward
- Your AWS account ID
Create a Cloud pipeline with the CloudWatch Pack
Create a new Edge Delta Cloud pipeline:
- Click Pipelines.
- Click New Pipeline.
- Select Cloud
- Specify a name to identify the pipeline.
- Select Compute Units based on your estimated traffic volume. This is the maximum bandwidth the agent can handle before signalling an error. The number of compute units used per hour counts towards your plan usage.
- Click Deploy Cloud Pipeline.
After the pipeline is deployed, apply the CloudWatch Pack to configure the pipeline for CloudWatch log processing. The Pack handles JSON unrolling, attribute parsing, and timestamp extraction automatically.
Copy the HTTPS endpoint from the Cloud pipeline settings. You need this endpoint when deploying the forwarder.
Deploy the Lambda Forwarder
Deploy from the AWS Serverless Application Repository
The simplest way to deploy the forwarder is through the AWS Serverless Application Repository (SAR). SAR creates the Lambda function and its IAM role automatically.
- Open AWS Serverless Application Repository and click Available Applications.
- Select Show apps that create custom IAM roles or resource policies. The forwarder apps are hidden unless this checkbox is selected.
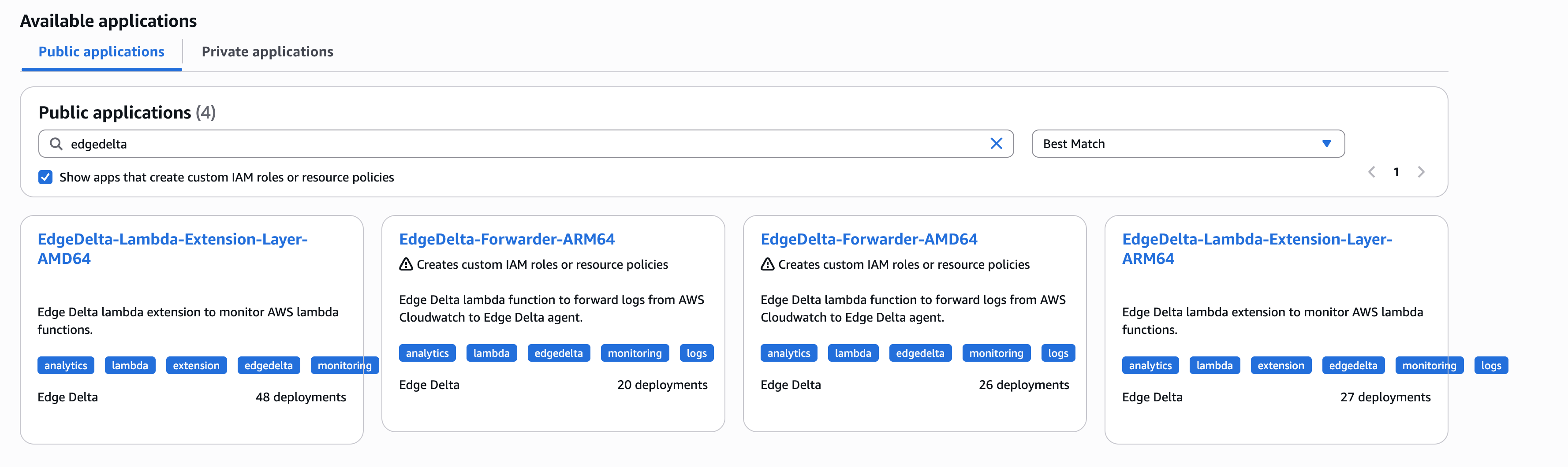
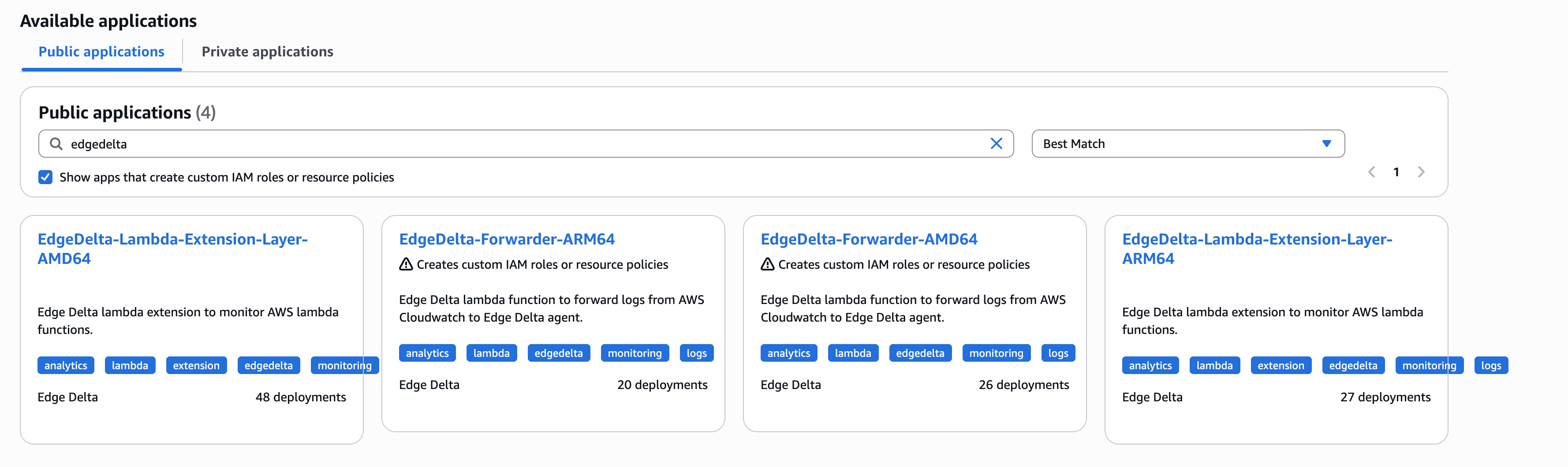
- Search for EdgeDelta and select the forwarder (either ARM64 or AMD64).
- During deployment, you will be prompted to:
- Enter a custom function name for your Lambda forwarder
- Confirm the function template settings
- Enter the HTTPS endpoint for the Cloud pipeline that you copied earlier.
- Click I acknowledge that this app creates custom IAM roles or resource policies.
- Click Deploy.
Note: The function can be deployed multiple times by providing different function names during deployment. Deploying with an existing function name upgrades the existing deployment if an upgrade is available.
Deploy manually
If you need to customize the IAM role or build process, you can deploy the forwarder manually from the edgedelta-forwarder repository.
Build the forwarder
- Clone the repository:
git clone https://github.com/edgedelta/edgedelta-forwarder.git
cd edgedelta-forwarder
- Build the executable:
GOOS=linux GOARCH=amd64 CGO_ENABLED=0 go build -tags lambda.norpc -o bootstrap main.go
- Zip the binary:
zip edgedelta-forwarder.zip bootstrap
Create an IAM role
Create an IAM role for the forwarder Lambda function with the following trust policy:
{
"Version": "2012-10-17",
"Statement": [
{
"Effect": "Allow",
"Principal": {
"Service": "lambda.amazonaws.com"
},
"Action": "sts:AssumeRole"
}
]
}
Save this as trust-policy.json and create the role:
aws iam create-role \
--role-name "my-forwarder-role" \
--assume-role-policy-document file://trust-policy.json
Attach the basic Lambda execution policy:
aws iam attach-role-policy \
--role-name "my-forwarder-role" \
--policy-arn "arn:aws:iam::aws:policy/service-role/AWSLambdaBasicExecutionRole"
Create a policy for the forwarder’s additional permissions. The forwarder calls lambda:GetFunction on every invocation to collect function metadata. The tag:GetResources permission is required when any of the ED_FORWARD_*_TAGS environment variables are enabled.
Save the following as forwarder-policy.json:
{
"Version": "2012-10-17",
"Statement": [
{
"Sid": "GetFunctionAccessPolicy",
"Effect": "Allow",
"Action": "lambda:GetFunction",
"Resource": "*"
},
{
"Sid": "TagReadOnlyAccessPolicy",
"Effect": "Allow",
"Action": "tag:GetResources",
"Resource": "*"
}
]
}
Attach the policy to the role:
aws iam put-role-policy \
--role-name "my-forwarder-role" \
--policy-name "ForwarderPolicy" \
--policy-document file://forwarder-policy.json
Create the Lambda function
Run the following command, replacing the placeholder values with your own:
aws lambda create-function \
--function-name "my-ed-forwarder" \
--runtime provided.al2 \
--handler bootstrap \
--role "arn:aws:iam::123456789012:role/my-forwarder-role" \
--zip-file "fileb://edgedelta-forwarder.zip"
After the function is created, set the ED_ENDPOINT environment variable to the Cloud pipeline HTTPS endpoint you copied earlier:
aws lambda update-function-configuration \
--function-name "my-ed-forwarder" \
--environment "Variables={ED_ENDPOINT=https://your-pipeline-endpoint}"
Assign Lambda invoke permission
The forwarder needs permission to be invoked by the CloudWatch Logs service.
CLI:
Run the following command, replacing the placeholder values with your own:
aws lambda add-permission \
--function-name "my-ed-forwarder" \
--statement-id "AllowCloudWatchInvoke" \
--principal "logs.amazonaws.com" \
--action "lambda:InvokeFunction" \
--source-arn "arn:aws:logs:us-west-2:123456789012:log-group:/aws/lambda/my-app:*" \
--source-account "123456789012"
Console:
- Open the Lambda console and select your forwarder function.
- Click Configuration, then click Permissions.
- Scroll to Resource-based policy statements and click Add permissions.
- Select AWS service, choose Other for the service, and enter
logs.amazonaws.comas the principal. - Set the action to
lambda:InvokeFunction. - Enter the log group ARN as the source ARN.
Create a subscription filter
A subscription filter triggers the forwarder whenever new logs are written to the target log group.
Note: The forwarder must be in the same AWS region as the log group. If you forward logs from multiple regions (for example, WAF logs in
us-east-1and application logs inus-west-2), deploy a separate forwarder in each region.
CLI:
Run the following command, replacing the placeholder values with your own:
aws logs put-subscription-filter \
--log-group-name "/aws/lambda/my-app" \
--filter-name "edge-delta-forwarder" \
--filter-pattern "" \
--destination-arn "arn:aws:lambda:us-west-2:123456789012:function:my-ed-forwarder"
Set --filter-pattern to "" (empty string) to forward all logs, or specify a CloudWatch filter pattern to forward only matching logs.
Console:
- Open the CloudWatch console and click Log groups.
- Select the log group you want to forward.
- Click the Subscription filters tab, then click Create Lambda subscription filter.
- Select your forwarder Lambda function as the destination.
- Specify a filter name. Leave the filter pattern empty to forward all logs.
- Click Start streaming.
Environment variables
Configure the following environment variables on the forwarder Lambda function. Set ED_ENDPOINT during deployment (SAR prompts for it automatically; for manual deployments, see the deploy steps above). You can configure additional variables in the Lambda console under Configuration > Environment variables.
| Variable | Required | Default | Description |
|---|---|---|---|
ED_ENDPOINT | Yes | Edge Delta Cloud pipeline HTTPS endpoint | |
ED_BATCH_SIZE | No | 1000000 | Maximum batch size in bytes for log payloads |
ED_SOURCE_TAG_PREFIXES | No | "" | Comma-separated prefixes to filter source tags |
ED_FORWARD_FORWARDER_TAGS | No | false | Fetch the forwarder Lambda’s own tags. Requires tag:GetResources and lambda:GetFunction permissions. |
ED_FORWARD_LOG_GROUP_TAGS | No | false | Fetch log group tags. Requires tag:GetResources permission. |
ED_FORWARD_SOURCE_TAGS | No | false | Fetch source resource tags by building an ARN from the log group name. Requires tag:GetResources permission. For Lambda sources, also requires lambda:GetFunction and the log group must follow the /aws/lambda/<function_name> naming convention. |
ED_PUSH_TIMEOUT_SEC | No | 10 | Seconds to wait between sending batches |
ED_RETRY_INTERVAL_MS | No | 100 | Initial retry interval in milliseconds. Increases exponentially on failure. |
Supported resources and tag fetching
The Forwarder supports CloudWatch logs from any AWS service. It automatically fetches resource tags for the following services:
- Lambda
- Fargate
- ECS
- EC2
- SNS
The following services have experimental tag-fetching support:
- RDS (MariaDB, MySQL, PostgreSQL)
- API Gateway (REST and HTTP)
- Step Functions (
/aws/vendedlogs/states) - DMS
- FSx for Windows
- AppSync
- CodeBuild
- Kinesis
- DocumentDB
- EKS
- Network Firewall
- Route 53
- VPC Flow Logs
- CloudTrail
- MSK
- Elasticsearch
- Transit Gateway
- Verified Access
Log group naming conventions for tag fetching
The Forwarder builds resource ARNs from log group names to fetch tags. The following table shows the expected log group format for each service:
| Service | Expected log group format | Tags fetched |
|---|---|---|
| Lambda | /aws/lambda/{function_name} | Function tags |
| SNS | /aws/sns/{topic_name} | Topic tags |
| ECS (cluster only) | /ecs/{cluster_name} | Cluster tags |
| ECS (cluster and service) | /ecs/{cluster_name}/{service_name} | Cluster and service tags |
| EC2 instance | /ec2/instance/{instance_id} | Instance tags |
| EC2 VPC | /ec2/vpc/{vpc_id} | VPC tags |
| Other services | /aws/{service}/{resource_name} | Best-effort ARN construction |
Verify the deployment
After completing the setup, verify that logs flow from CloudWatch to Edge Delta:
- Generate test traffic in your source application, or wait for natural log activity.
- In the AWS Lambda console, open the forwarder function and check the Monitor tab. Verify that the function is being invoked.
- Check the forwarder’s own CloudWatch log group (
/aws/lambda/<forwarder_name>) for errors. - In the Edge Delta console, open the Cloud pipeline and confirm that logs appear in the live view.
- Optionally, test the Cloud pipeline endpoint directly:
curl -X POST "https://your-pipeline-endpoint" \
-H "Content-Type: application/json" \
-d '{"message": "test"}'
A successful response returns HTTP 202.
Troubleshooting
| Symptom | Cause | Solution |
|---|---|---|
| Forwarder is not invoked | Missing subscription filter or invoke permission | Verify both exist: aws logs describe-subscription-filters --log-group-name "/aws/lambda/my-app" |
| Logs appear in CloudWatch but not in Edge Delta | Incorrect ED_ENDPOINT or Cloud pipeline not running | Confirm the endpoint URL is correct and returns HTTP 202 with a curl test |
| Logs dropped after pipeline transform | body set to empty string in OTTL transform | Use a placeholder value like "-" instead. Edge Delta drops logs with empty body fields. |
| Tags not appearing on logs | Missing IAM permissions | Ensure the forwarder role has tag:GetResources. For Lambda sources, also add lambda:GetFunction. |
| Cross-region logs not arriving | Forwarder deployed in a different region than the log group | Deploy a separate forwarder in the same region as the log group |
Benchmarks
A single Lambda Forwarder sends batches of 200 to 300 KB. One Cloud pipeline processes approximately 10 MB per minute of forwarder traffic. For higher throughput, deploy additional Cloud pipelines or use the Lambda Extension, which sends larger batches (10 to 20 MB).
Best practices for reducing log volume
The Forwarder sends everything that arrives from CloudWatch, so reducing volume at the source keeps both CloudWatch and Cloud pipeline costs lower:
- Set log group retention policies. CloudWatch retains logs indefinitely by default. Set a retention period (for example, 30 days) on each forwarded log group to prevent storage costs from compounding. You can configure retention in the CloudWatch console or with
aws logs put-retention-policy. - Use subscription filter patterns. When you create a subscription filter, specify a filter pattern instead of forwarding all logs. For example, filter for ERROR and WARN level entries to exclude routine DEBUG output from reaching the Cloud pipeline.
- Configure log levels on source functions. Restrict production Lambda functions to WARN or ERROR level logging. Reducing log output at the source cuts CloudWatch ingestion costs and reduces the volume the Forwarder sends to your Cloud pipeline.
- Apply structured logging at the source. Configure source functions to output native JSON logs (supported in Python 3.8+, Node.js 18+, and Java 11+). Structured logs are easier to filter with CloudWatch subscription patterns and parse more reliably in the Cloud pipeline.